Why Every Small Business Should Run a Penetration Test Before It’s Too Late
If a hacker broke into your business today, would you even know?
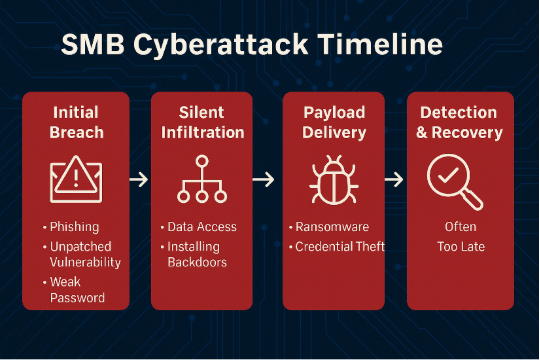
The truth is, most small businesses don’t realize they’ve been breached until weeks or months later—when customer data is leaked, systems crash, or bank accounts start draining.
There’s one fast and affordable way to check your defenses before disaster strikes: penetration testing (aka a simulated cyberattack on your systems by professionals you trust).
In this blog, we’ll show you how penetration testing works, what it reveals, and why every small business should be doing it—especially before cyber insurance, regulators, or angry clients come calling.
🔍 What Is Penetration Testing?
Penetration testing (or pen testing) is an ethical form of hacking where a trusted IT security team simulates a real-world cyberattack—just to see how far they can get.
The goal? Find vulnerabilities before real hackers do.
Think of it as a fire drill for your network—except instead of practicing your response, you're proactively finding the exits that were accidentally left open.
✅ One Quick Way to Spot Cyber Risk

Why does this matter for SMBs? Because hackers today don’t discriminate by business size. In fact:
- 43% of all cyberattacks target small businesses
- 60% of SMBs go out of business within 6 months of a breach
Penetration testing helps prevent this by:
- Uncovering weak passwords
- Exposing open ports or outdated software
- Simulating phishing or ransomware entry points
- Showing exactly how attackers could bypass your current tools
💡 5 Benefits of Penetration Testing for Your Business
1. Know What a Hacker Could Exploit
You’ll see your network the way a hacker does—and get a prioritized list of what to fix right now.
2. Save Money by Preventing Downtime
Data breaches can cost $250,000+ for small businesses. Pen testing helps you avoid costly surprises.
3. Support Your Internal IT Team
Give your IT staff real data to plan smarter upgrades, patch faster, and justify budgets.
4. Stay Compliant with Cyber Regulations
HIPAA, PCI, FTC Safeguards, and even cyber insurance providers increasingly require periodic testing.
5. Strengthen Client Trust
Showing you’ve invested in proactive security builds trust and separates you from less-prepared competitors.
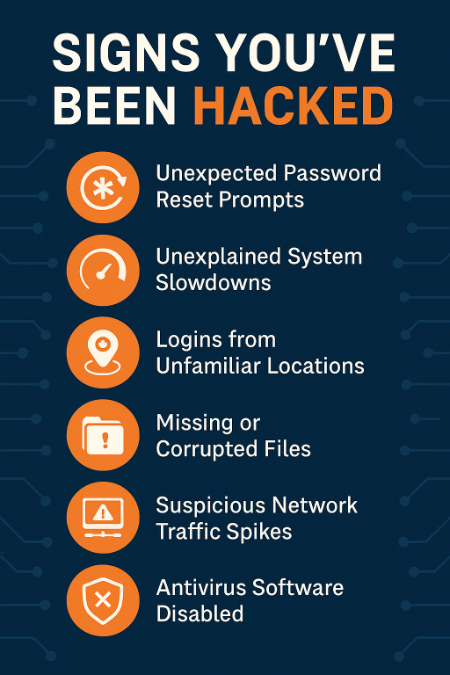
⚠️ Wait… Could Hackers Already Be Inside?
Here’s the scary part: attackers often lurk in systems for over 200 days before being discovered (source: IBM). That’s enough time to:
- Steal data
- Deploy ransomware
- Spy on internal communications
- Compromise client accounts
Penetration testing gives you the visibility to detect hidden threats—before they cost you everything.
🔐 How ICG Helps You Test (and Fix) Your Defenses
At ICG, we help small businesses across Miami and South Florida run secure, scoped, and budget-friendly pen tests. We make it simple:
- No geek speak
- No unnecessary add-ons
- Actionable findings, plain-English reports
- Help fixing every issue we find
Whether you have in-house IT or none at all, we guide your team through every step—from the simulated attack to full remediation.
🚀 Ready to Find Out If You’re at Risk?
🔍 Schedule your FREE consult now
📜 Ask about our Pen Test + Remediation Package
🌐 Visit www.icgi.com to learn more
Don’t wait for a breach to find your blind spots. Test now. Fix now. Breathe easier.
.png)



